The New Cyber Battlefield: How Advanced Attacks Are Targeting India’s Banking Sector
Cyber warfare is no longer a distant threat—it is actively unfolding, and now it is hitting closer to home.
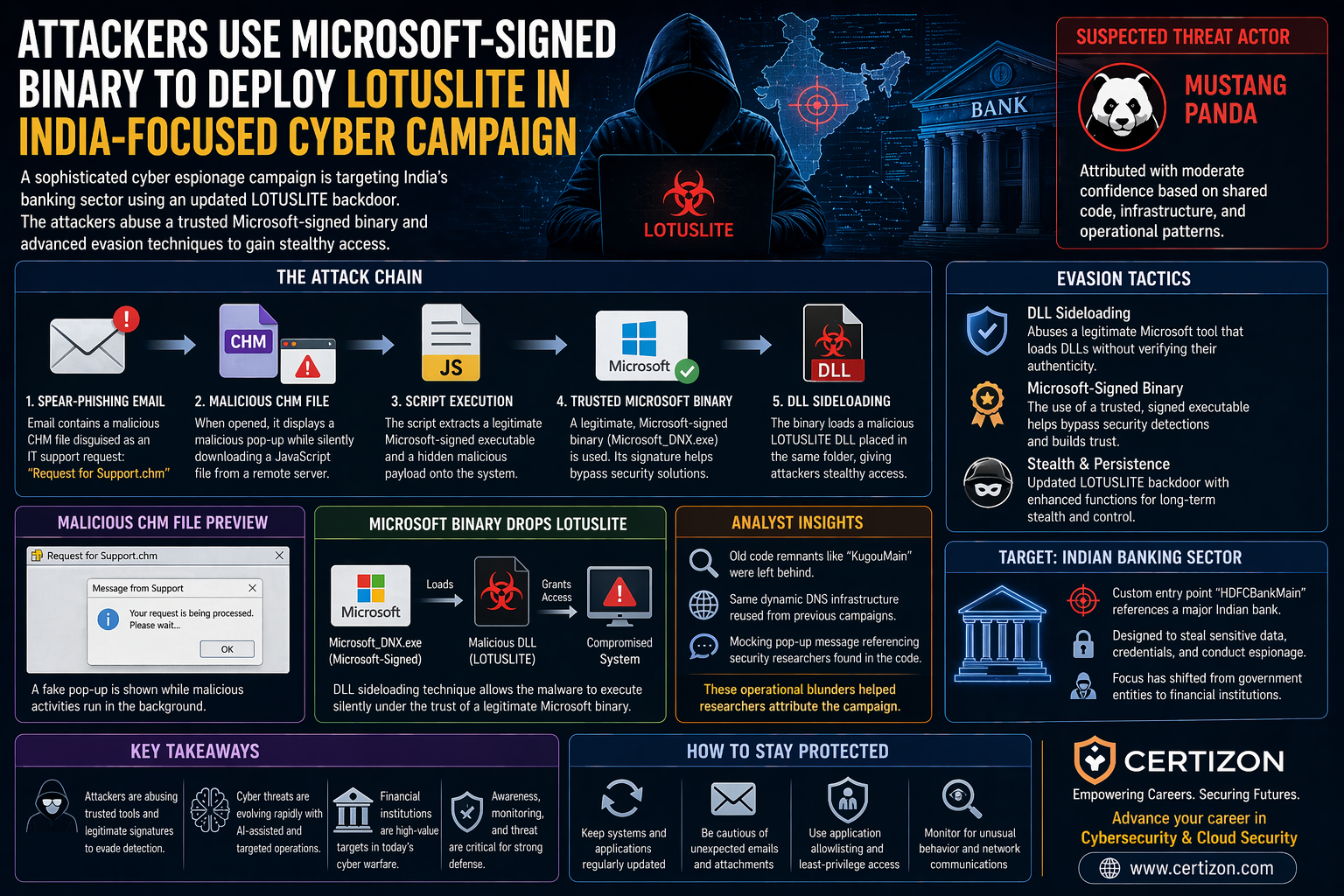
A recent cyber espionage campaign targeting India’s banking sector has revealed how sophisticated and strategic modern cyberattacks have become. Researchers have identified the use of an upgraded LOTUSLITE backdoor, deployed through highly deceptive techniques designed to bypass even advanced security systems.
What makes this attack particularly concerning is not just the target—but the method.
🎯 A Shift in Target: From Governments to Banks
Traditionally, advanced persistent threat (APT) groups focused on government institutions and defense systems. However, this campaign signals a major shift.
The suspected group behind this attack, Mustang Panda, is now targeting financial institutions—highlighting the growing importance of the banking sector in cyber warfare.
This shift reflects a broader trend:
- Financial systems = economic power
- Data = strategic asset
- Banks = high-value targets
⚙️ How the Attack Works (Simplified)
The attack chain is carefully designed to appear legitimate at every step, making detection extremely difficult.
It begins with a spear-phishing email—a highly targeted message sent to employees. The email contains a file disguised as a routine IT support request.
📌 Attack Flow:
- A fake file named “Request for Support.chm” is sent
- The file displays a harmless-looking pop-up
- In the background, it downloads malicious scripts
- A trusted Microsoft-signed executable is deployed
- The system unknowingly loads a hidden malware (LOTUSLITE)
This entire process happens silently, giving attackers stealthy access to the system.
🧠 The Smart Trick: Using Trusted Microsoft Tools
One of the most dangerous aspects of this attack is the use of a legitimate Microsoft-signed file.
Attackers used a trusted executable:
- Microsoft_DNX.exe
Because it carries a valid digital signature, most security systems assume it is safe.
However, attackers exploited a weakness in how this tool loads files. Using a technique called DLL sideloading, they trick the system into loading a malicious file instead of a legitimate one.
➡️ Result:
A trusted application becomes a gateway for malware
🦠 LOTUSLITE: Smarter, Stealthier, More Dangerous
The updated version of the LOTUSLITE backdoor shows clear signs of evolution.
Key Enhancements:
- Increased complexity (22 export functions vs earlier 16)
- Custom entry point named “HDFCBankMain” (target-specific coding)
- Improved evasion techniques to avoid detection
These changes indicate that attackers are now:
- Customizing malware for specific targets
- Investing in long-term access rather than quick attacks
⚠️ Even Attackers Make Mistakes
Interestingly, despite the sophistication, researchers identified operational errors that exposed the attackers.
- Old code fragments like “KugouMain” were left behind
- Same infrastructure (DNS services) reused from earlier campaigns
- Embedded messages mocking security researchers
These mistakes helped analysts connect the attack to known threat actors.
☁️ What This Means for Cloud & Security
Modern banking systems rely heavily on cloud platforms like:
- Amazon Web Services
- Google Cloud
- Microsoft Azure
While cloud offers scalability and resilience, attacks like this show:
🚀 Strength:
- Faster detection and monitoring
- Centralized security controls
- Scalable defense systems
⚠️ Risk:
- One compromised endpoint can affect larger systems
- Trusted software can be exploited
- Human error remains a major vulnerability
🔐 The Bigger Lesson
This attack highlights a critical truth about modern cybersecurity:
The biggest threats no longer come from unknown tools—but from trusted systems being misused.
It also reinforces that:
- Cyber warfare is becoming more targeted
- Financial institutions are now frontline targets
- Attackers are blending social engineering + technical exploits
🧠 Key Takeaways
- Cyberattacks are becoming highly targeted and stealthy
- Trusted software can be weaponized against organizations
- Financial institutions are a primary focus of APT groups
- Detection is becoming harder due to AI and advanced evasion techniques
- Cybersecurity must evolve from prevention → intelligent defense
💡 Conclusion
This isn’t just another cyberattack—it’s a glimpse into the future of digital warfare.
Attackers are no longer breaking in.
They are being invited in—through trust, deception, and human error.
And in this new battlefield, awareness is just as important as technology.
