Threat Landscape March 2026: Ransomware, Data Leaks & AI-Driven Cyber Attacks on the Rise
Cyber threats are evolving faster than ever—and March 2026 proved just how aggressive and organized the modern threat landscape has become.
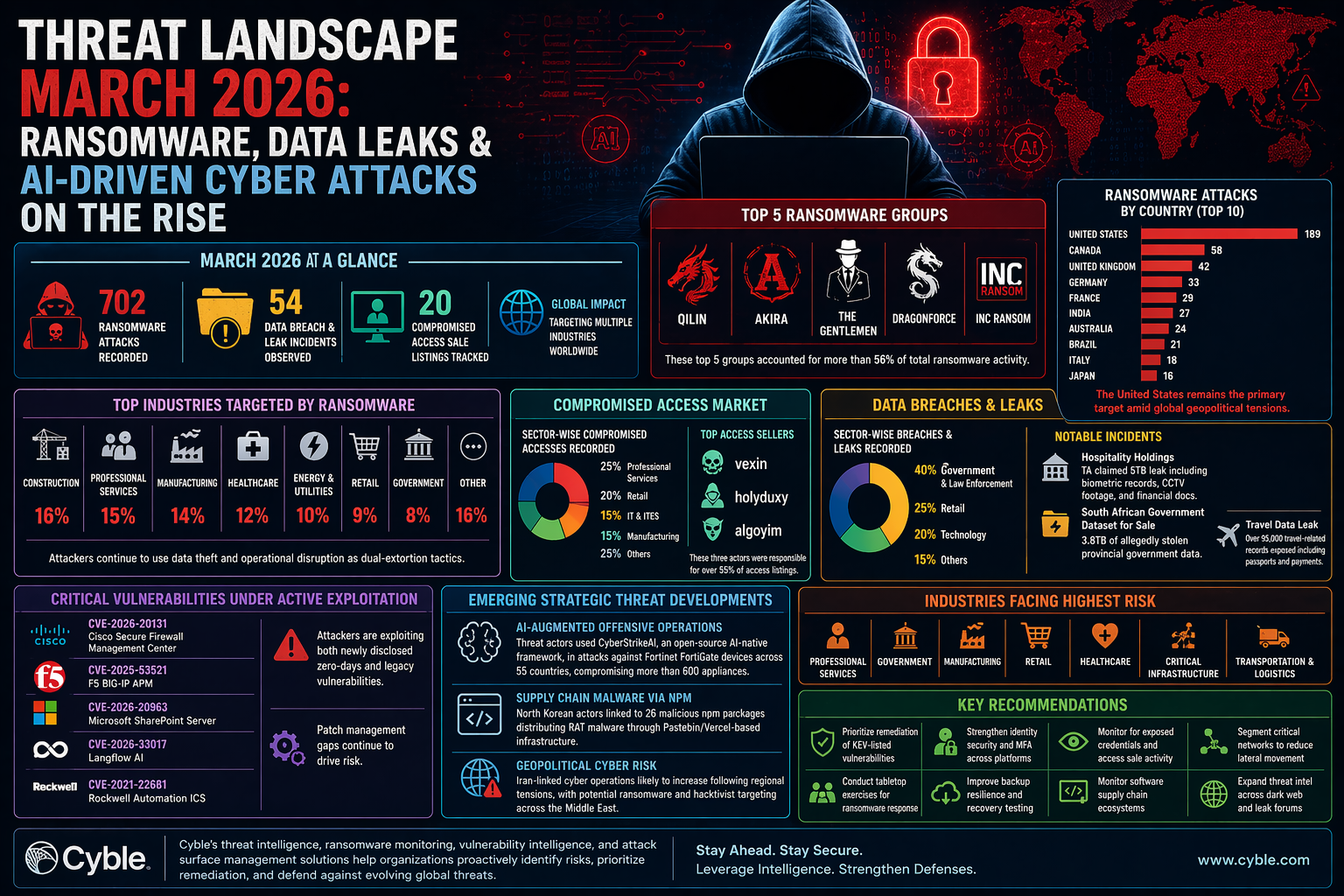
According to insights from Cyble Research and Intelligence Labs, the global cybersecurity environment saw a sharp surge in ransomware attacks, data breaches, access broker activity, and critical vulnerability exploitation.
🚨 A Snapshot of March 2026 Threat Activity
The numbers tell a concerning story:
- 702 ransomware attacks recorded globally
- 54 major data breach and leak incidents
- 20 compromised access listings on cybercrime forums
These trends highlight a mature cybercrime ecosystem where attackers are no longer working in isolation—but collaborating in structured, scalable operations.
🔐 Ransomware Continues to Dominate
Ransomware remained the most significant threat in March 2026, with attackers combining data theft and operational disruption for maximum impact.
Most Active Ransomware Groups:
- Qilin
- Akira
- The Gentlemen
- Dragonforce
- INC Ransom
These groups accounted for over 56% of total ransomware activity, showcasing their dominance and organized affiliate networks.
🏭 Industries Under Attack
Cybercriminals focused heavily on sectors that:
- Handle sensitive data
- Require high uptime
- Have complex infrastructure
Most Targeted Industries:
- Construction
- Professional Services
- Manufacturing
- Healthcare
- Energy & Utilities
These industries are prime targets because downtime directly translates into financial and operational losses.
🧩 Rise of Access Brokers
One of the most critical trends observed was the growth of initial access brokerage markets.
Attackers are no longer just breaching systems—they are selling access to other criminals.
Key Insights:
- 20 access sale incidents tracked
- Top sectors: Professional Services (25%), Retail (20%)
- Major actors: vexin, holyduxy, algoyim
👉 This model allows ransomware groups to skip the initial hacking phase and directly exploit compromised networks.
💸 Data Breaches & Leak Markets Stay Active
Data theft remains a core objective for cybercriminals.
Key Observations:
- 54 major breach incidents
- High targeting of Government, Retail, and Technology sectors
Notable Incidents:
- 5TB data leak claimed from a hospitality group
- 3.8TB government dataset put up for sale
- 95,000+ travel records exposed
👉 Data is now a primary currency in cybercrime, often used for extortion or resale.
⚠️ Critical Vulnerabilities Being Exploited
Attackers are actively targeting both new and old vulnerabilities, especially those listed in known exploited catalogs.
Notable Exploited Systems:
- Cisco Secure Firewall Management Center
- F5 BIG-IP APM
- Microsoft SharePoint Server
- Langflow AI
👉 The biggest issue?
Many organizations are still failing at timely patch management.
🤖 Emerging Threat Trends
1. AI-Powered Cyber Attacks
Threat actors are leveraging AI tools like CyberStrikeAI to automate and scale attacks.
2. Supply Chain Attacks
Malicious npm packages linked to state-sponsored actors are being used to distribute malware.
3. Geopolitical Cyber Risks
Rising tensions, especially involving Iran-linked groups, are influencing global cyber activity.
🎯 High-Risk Sectors Going Forward
Organizations in the following sectors face the highest risk:
- Professional Services
- Government
- Manufacturing
- Retail
- Healthcare
- Critical Infrastructure
- Logistics & Transportation
These sectors combine valuable data, complex systems, and operational dependency—making them attractive targets.
🛡️ Key Security Recommendations
To defend against these evolving threats, organizations must:
- Prioritize patching of critical vulnerabilities
- Enforce strong identity security and MFA
- Monitor for leaked credentials and access sales
- Segment networks to prevent lateral movement
- Conduct ransomware response simulations
- Strengthen backup and recovery strategies
- Monitor software supply chains
- Invest in threat intelligence and dark web monitoring
Conclusion
The March 2026 threat landscape reveals a clear pattern:
👉 Cybercrime is now industrialized, collaborative, and highly strategic
Attackers are combining:
- Ransomware
- Data theft
- Access brokerage
- AI-driven tools
This creates a high-risk environment for organizations worldwide.
The question is no longer if your organization will be targeted—
👉 it’s how prepared you are to detect, respond, and recover.
